This is where you try to paint yourself in a box. That's not going to happen here. Sometimes I wander beyond the lines of a typical copywriter. I dabble in content strategy, search, etymology, branding, research, history, green technology, alternative fuels - and a whole lot more. Hope it's an enjoyable read.
Wednesday, January 27, 2010
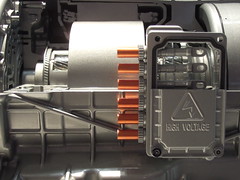
High Voltage Transmission Detail
Cutaway of GM's Two-Mode Hybrid transmission. Supplemental power comes from two 60kW motors housed within the electronically variable transmission. The two electric motors work in tandem with four fixed gears to distribute both gasoline and electric power as needed. The electric motors have two distinct modes of operation depending upon city or highway driving and can use the electric motors for boosting and regenerative braking. Claims include close to 40% fuel efficiency improvement in city driving. Chrysler and BMW Group formed a cooperative effort with GM called the Global Hybrid Cooperation, to help develop this next-generation tranny.
Monday, January 25, 2010
Let the takeover begin
If the Chinese business man Wang Chuanfu's goal is to lull us to sleep - he has succeeded. The styling is mundane and lackluster. But beware - under the hood of this dragon is Wang's deep desire to be China's top automaker by 2015. He plans on being #1 in the world by 2025. Unreasonable? Think again.
Build Your Dream (BYD) sold 450,000 vehicles in 2009 alone. China is pushing hard to "Go inland." That is - to sell in China first - then conquer the foreign lands. Vehicle sales are skyrocketing - The China Association of Automobile Manufacturers reported auto sales in second (41%) and third-tier (51%) cities surged for the first 9 months of 2009. Once fortified in China - watch out for the U.S. takeover.
BYD's display didn't have singers, dancers or any showstopping entertainment. But if there were one company to take note of this year - it is BYD. Sure they have to learn our culture and cater to our style and American needs (like large cupholders). But good design can be acquired as seen by Hyundai - when they hired Joel Piaskowski. In fact, Piaskowski was wooed away from Hyundai to Mercedes early last year.
BYD is the largest supplier of cell phone batteries in the world. Combine the worldly know-how with visionaries like Warren Buffet, who recently made a 10% investment in the nascent company and you can just see a glimmer of what's to come. When electric turns the corner in the states, BYD will be there.
There might even be an electric vehicle for sale by the end of 2010. With up to 205 miles between charges, and torque that rivals a Ford F-150 pickup truck, the e6 may have just enough performance for American's to overlook the dull appearance. Time will tell.
Build Your Dream (BYD) sold 450,000 vehicles in 2009 alone. China is pushing hard to "Go inland." That is - to sell in China first - then conquer the foreign lands. Vehicle sales are skyrocketing - The China Association of Automobile Manufacturers reported auto sales in second (41%) and third-tier (51%) cities surged for the first 9 months of 2009. Once fortified in China - watch out for the U.S. takeover.
BYD's display didn't have singers, dancers or any showstopping entertainment. But if there were one company to take note of this year - it is BYD. Sure they have to learn our culture and cater to our style and American needs (like large cupholders). But good design can be acquired as seen by Hyundai - when they hired Joel Piaskowski. In fact, Piaskowski was wooed away from Hyundai to Mercedes early last year.
BYD is the largest supplier of cell phone batteries in the world. Combine the worldly know-how with visionaries like Warren Buffet, who recently made a 10% investment in the nascent company and you can just see a glimmer of what's to come. When electric turns the corner in the states, BYD will be there.
There might even be an electric vehicle for sale by the end of 2010. With up to 205 miles between charges, and torque that rivals a Ford F-150 pickup truck, the e6 may have just enough performance for American's to overlook the dull appearance. Time will tell.
Friday, January 22, 2010
Electric / Hybrid Eye Candy
 Love the deep burnt orange color on Canadian-made eVaro electric / hybrid made by Future Vehicle Technologies (formerly Fuel Vapor Technologies). This fully-functioning plug-in electric series hybrid produces no emissions for 90% of its time on the road. It has an unlimited range with FVT custom on-board high-voltage generator.
Love the deep burnt orange color on Canadian-made eVaro electric / hybrid made by Future Vehicle Technologies (formerly Fuel Vapor Technologies). This fully-functioning plug-in electric series hybrid produces no emissions for 90% of its time on the road. It has an unlimited range with FVT custom on-board high-voltage generator.The University of Fraser Valley confirmed an amazing 275 mpg for city driving and an average 165 mpg for highway driving. But this is no slow-poke, eVaro has a top speed of 135 mph, and can go from 0 to 60 mph in a sizzling five seconds. Check out the eVaro testing tires on YouTube.
Thursday, January 21, 2010
Detroit Electric Vehicle Circa 1922
This 1922 Detroit Electric Car was originally owned by socialite Mrs. Joseph Ballard of Binghamton, New York from 1922 until 1934. The $2,985 price tag is equivalent to about $38,000 today.
 Mrs. Ford had an electric car just like this one - also on display at the Henry Ford Museum in Dearborn, MI. This car was on display at the 2010 North American international Auto Show in Detroit, Michigan.
Mrs. Ford had an electric car just like this one - also on display at the Henry Ford Museum in Dearborn, MI. This car was on display at the 2010 North American international Auto Show in Detroit, Michigan.
Electric cars were extremely popular with well-to-do women who had trouble, or didn't care for, the hand-cranking that was necessary with gasoline powered cars. One of the other key selling points: wealthy woman much preferred the electric cars roomy interiors that resembled parlors or powder rooms.

The performance wasn't bad for the day - top speed of 25mph and a range of up to 60 miles. In 1900 electric cars far outsold steam and gasoline powered cars, but that all changed with the electric starters on gasoline cars. In 1916, Detroit Electric made almost 1900 cars - that dropped dramatically to 143 cars in 1922 when this vehicle was made.
 Mrs. Ford had an electric car just like this one - also on display at the Henry Ford Museum in Dearborn, MI. This car was on display at the 2010 North American international Auto Show in Detroit, Michigan.
Mrs. Ford had an electric car just like this one - also on display at the Henry Ford Museum in Dearborn, MI. This car was on display at the 2010 North American international Auto Show in Detroit, Michigan.Electric cars were extremely popular with well-to-do women who had trouble, or didn't care for, the hand-cranking that was necessary with gasoline powered cars. One of the other key selling points: wealthy woman much preferred the electric cars roomy interiors that resembled parlors or powder rooms.

The performance wasn't bad for the day - top speed of 25mph and a range of up to 60 miles. In 1900 electric cars far outsold steam and gasoline powered cars, but that all changed with the electric starters on gasoline cars. In 1916, Detroit Electric made almost 1900 cars - that dropped dramatically to 143 cars in 1922 when this vehicle was made.
Friday, January 15, 2010
The Eve of a New Electric Infrastructure
Do a little research on electric cars and you'll find some interesting nuggets. One of the more startling facts: At the turn of the century, electric vehicles outnumbered gas-powered vehicles two to one! They had distinct advantages; they were easier to start, quieter, cleaner and required no gear shifting. That all changed with the advent of the electric starter.
The first self-starting ignition was used on a 1911 Cadillac and was invented by GM engineers Charles Kettering and Clyde Coleman. Bye bye hand cranking. The patent for the ignition coil was awarded in 1915. Kettering is best known as the founder of Delco (Dayton Engineering Laboratories Company).
But, even before Kettering was Nikola Tesla with his disruptive discharge "Electrical Igniter for Gas Engines" - awarded U.S. Patent 609,250 on August 16, 1898.
A. Atwater Kent patented the modern form of the ignition coil in 1921 along with contacts, distributor and single coil design.
Detroit Edison and MichCon have made an effort to steadily replace older supervisor vehicles with Ford Escape plug-in Hybrids. Ford recently announced in August of 2009 that they have developed an "intelligent vehicle-to-grid communication and control system for its plug-in hybrid vehicles that "talks" directly with the nation's electric grid." The new system allows the vehicles operator to program when to charge, for how long and at what utility rate.
Until the infrastructure of the country is upgraded, including electrical grid, car-charging outlets, battery swapping, etc. As reported in Green Tech, the California Bay Area along with Better Place is hoping to implement a massive $1 billion electronic infrastructure by 2012. Just like the advent of the electric ignition, this infrastructure will have to be easy-to-use, clean and convenient to succeed.
The first self-starting ignition was used on a 1911 Cadillac and was invented by GM engineers Charles Kettering and Clyde Coleman. Bye bye hand cranking. The patent for the ignition coil was awarded in 1915. Kettering is best known as the founder of Delco (Dayton Engineering Laboratories Company).
But, even before Kettering was Nikola Tesla with his disruptive discharge "Electrical Igniter for Gas Engines" - awarded U.S. Patent 609,250 on August 16, 1898.
A. Atwater Kent patented the modern form of the ignition coil in 1921 along with contacts, distributor and single coil design.
Detroit Edison and MichCon have made an effort to steadily replace older supervisor vehicles with Ford Escape plug-in Hybrids. Ford recently announced in August of 2009 that they have developed an "intelligent vehicle-to-grid communication and control system for its plug-in hybrid vehicles that "talks" directly with the nation's electric grid." The new system allows the vehicles operator to program when to charge, for how long and at what utility rate.
Until the infrastructure of the country is upgraded, including electrical grid, car-charging outlets, battery swapping, etc. As reported in Green Tech, the California Bay Area along with Better Place is hoping to implement a massive $1 billion electronic infrastructure by 2012. Just like the advent of the electric ignition, this infrastructure will have to be easy-to-use, clean and convenient to succeed.
Wednesday, January 13, 2010
THE ART OF (Electronic) WARfare

Zhi xinxi quan (制信息权) – establishing information dominance.

I learned a lot about space warfare and the United States vulnerability to attack when working for Dawn Satellite. We sold satellite equipment to military and government institutions as well as other commercial agencies. The United States is so dependent on space and the satellites that provide our information that any successful attack would shock and blind us into a stupor. According to the Report of the Commission to Assess Unites States National Security Space Management and Organization, "the U.S. is more dependent on space than any other nation." This whilst China's capabilities have advanced exponentially since the late 1990's.
Much of our military machinery is dependent on the Department of Defense controlled Global Positioning System (GPS) which could be knocked out and affect everything from Wall Street and ATM machines to our high-tech air-defense systems.
Increasingly, Chinese military strategists have come to view information dominance as the precursor for overall success in a conflict. Accordingly the People's Liberation Army (PLA) is preparing to establish information dominance and control all adversary’s information flow which is considered a fundamental prerequisite for seizing naval and air superiority during a time of war. This mirrors the United States philosophy stated in the Joint Vision 2010 that states “information dominance” is the key to any military victory. U.S. Space Command (now US Stratcom) documents expound upon the United States desire to control and own space through space superiority. The U.S. does not want to participate in any arms control covering space – or reduction of space weaponization. In effect we are elevating outer space as the newest arena for military confrontation and setting the table for a new arms race of astronomical proportions.
key to any military victory. U.S. Space Command (now US Stratcom) documents expound upon the United States desire to control and own space through space superiority. The U.S. does not want to participate in any arms control covering space – or reduction of space weaponization. In effect we are elevating outer space as the newest arena for military confrontation and setting the table for a new arms race of astronomical proportions.
 key to any military victory. U.S. Space Command (now US Stratcom) documents expound upon the United States desire to control and own space through space superiority. The U.S. does not want to participate in any arms control covering space – or reduction of space weaponization. In effect we are elevating outer space as the newest arena for military confrontation and setting the table for a new arms race of astronomical proportions.
key to any military victory. U.S. Space Command (now US Stratcom) documents expound upon the United States desire to control and own space through space superiority. The U.S. does not want to participate in any arms control covering space – or reduction of space weaponization. In effect we are elevating outer space as the newest arena for military confrontation and setting the table for a new arms race of astronomical proportions.
If the U.S. satellite constellations in the middle Earth orbits (MEO) altitudes could be rendered unavailable by the Chinese we would effectively be neutered. To be sure, we are developing counter measures including the Rapid Attack Identification Detection Reporting System (Raidrs) Block 20 direct-ascent anti-satellite weapon. Whether jamming or disabling a number of GPS satellites, the U.S. dependence on technology could be its Achilles heel. China reportedly assisted in the development of the European Union’s Galileo satellite navigation system, a 30-satellite system alternate to the U.S. GPS system. Since the Galileo system is up and running the U.S. effectively loses a valuable strategic dominant high ground it alone has owned for over three decades. The U.S. pushed hard to see that China did not have access to the Galileo system. The Chinese Beidou Navigation System (BNS), also known as Compass, is scheduled to have all 35 satellites operational by 2015. If the Chinese Navigation system isn’t up and running yet – how do they guide their powerful Dong Feng 21 missles? The Chinese special "Kill Weapon" is designed to destroy U.S. aircraft carriers at a distance up to 2000km in less than 12 minutes. According to the United States Naval Institute (USNI), “China is relying on a complex guidance system, low radar signature and maneuverability that makes its [Dong Feng Missile] flight path unpredictable.” USNI states, “Supporting the missile is a network of satellites, radar and unmanned aerial vehicles that can locate U.S. ships and then guide the weapon, enabling it to hit moving targets.”
The U.S. Strategic Commandand Air Force Space Command just announced on 7 January 2010, the existing GPS constellation system will be enhanced with new GPS satellites to be placed in orbit and allow a reshuffling of the deck so there will be better worldwide coverage - including blind-spots in Afghanistan. This redundancy policy should bode well in the event of a Chinese attack on the existing system. According to USSTRATCOM, "the number of GPS satellites in view from any point on earth will increase, potentially increasing accuracy of GPS receivers."
China’s is actively researching and testing new technologies to thwart satellite transmissions including: jamming, use ground-based laser Dazzlers, launch an anti-satellite weapon (ASAT), use electromagnetic pulse (EMP) bursts, piggy-back satellites, micro satellites, or spoofing (sending fake signals that appear authentic) is its ability to infiltrate and disrupt U.S. computer networks.
Which leads us to Google andthe tip of the iceburg. According to David Drummond, the company's chief legal representative, "In mid-December, we detected a highly sophisticated and targeted attack on our corporate infrastructure originating from China that resulted in the theft of intellectual property from Google." Google went on to state that at least 20 other large companies were similary targeted. No direct accusation was made that attributed the theivery to the Chinese government, but if you read between the lines it is fairly evident Google thinks so since the targeted gmail accounts were tied to Chinese dissidents. New York Times interviewed Wengi Gao, the Chinese Consulate spokesman in New York who stated,"The Chinese government is opposed to and strictly forbids any cybercrime." Google has a little over 20 percent of the Chinese market share, so pulling out completely is saying a lot about the gravity of this incident.
GhostNet, a cyber-espionage network, hacked into government, corporate and private computers in 103 countries. According to Nart Villeneuve's "Tracking GhostNet: Investigating a Cyber Espionage Network" report, "Up to 30% of the infected hosts are considered high-value targets and include computers located at ministries of foreign affairs, embassies, international organizations, news media, and NGOs." Of key importance to U.S. intelligence is whether or not Chinese "black hat" programmers may be supplying or actively working for the Chinese government - giving them zero day exploit capabilities. Although the GhostNet report did not accuse the Chinese government of spying, the University of Cambridge Computer Laboratory researches did in their Technical Report #746, "The snooping dragon: social-malware surveillance of the Tibetan movement." They state in their conclusion, "In this note we described how agents of the Chinese government compromised the computing infrastructure of the Office of His Holiness the Dalai Lama."
The Capability of the People's Republic of China to Conduct Cyber Warfare and Computer Network Exploitation report mentioned earlier states the Chinese strategy is characterized by the combined employment of network warfare tools and electronic warfare weapons against an adversary’s information systems in the early phases of a conflict. A one-two punch.
What we are seeing is the advent of a new spy regime digging in the trenches for a possible Cyber War. Strategically placed "bombs" are scattered in "blind spots" in key institutions and government agencies that PLA forces could exploit at predetermined times or as the tactical situation warranted.
What we are seeing is the advent of a new spy regime digging in the trenches for a possible Cyber War. Strategically placed "bombs" are scattered in "blind spots" in key institutions and government agencies that PLA forces could exploit at predetermined times or as the tactical situation warranted.
According to the seminal "The Art of War" by Sun Tzu section 13 on the use of spies, there are five classes. The fifth class is surviving spies, "who bring back news from the enemy's camp." It is the surviving spy's information that can be used on appointed occasions. Finding the weakness of the enemy and exploiting it at the most convenient time. They say that if you put a frog into a pot of boiling water, it will leap out right away to escape the danger. But, if you put a frog in a kettle that is filled with water that is cool and pleasant, and then you gradually heat the kettle until it starts boiling, the frog will not become aware of the threat until its too late. Things are heating up. And the way things are going, I'm more worried about China then the melting of the polar ice cap.
Subscribe to:
Posts (Atom)